In an earlier blog I walked through various options on how to use Microsoft Authenticator with Workspace ONE Access (formerly known as VMware Identity Manager). In the final option, we talked about using the Microsoft Azure MFA Server. However, as of July 1st, 2019, Microsoft is no longer offering the MFA Server for new deployments.
Microsoft does however provide another option to leverage Azure MFA by using the Network Policy Server extension for Azure.
In the blog I will walk through the process of configuring a Network Policy Server along with the NPS Extension.
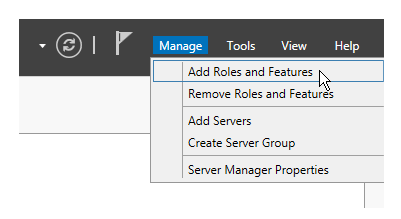
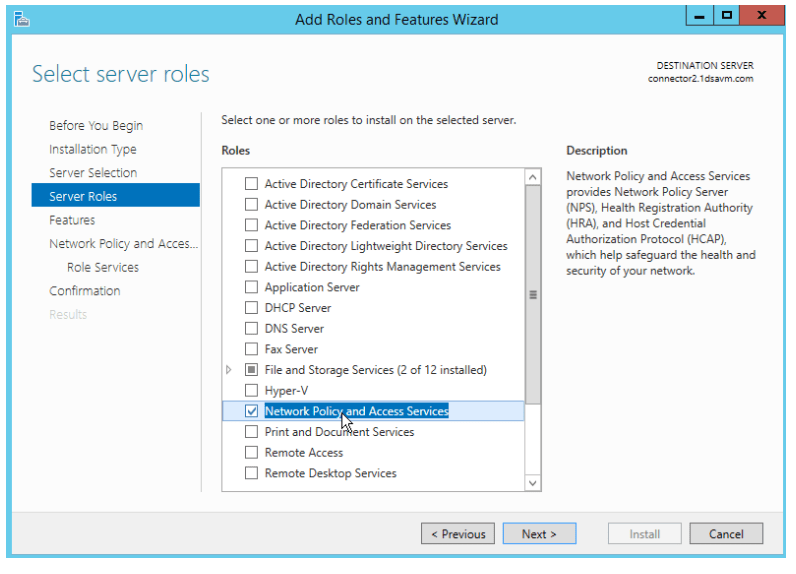
Install and Configure the Network Policy Server
- Using the Server Manager -> Add Role and Features
- Click Next
- Select Role-Based or feature-based Installation
- Select the Server from the Server Pool and click next
- Add the Network Policy and Access Services
- Add the dependency features.
- Add the Network Policy Server
- Complete the rest of the wizard to install the Network Policy Server.
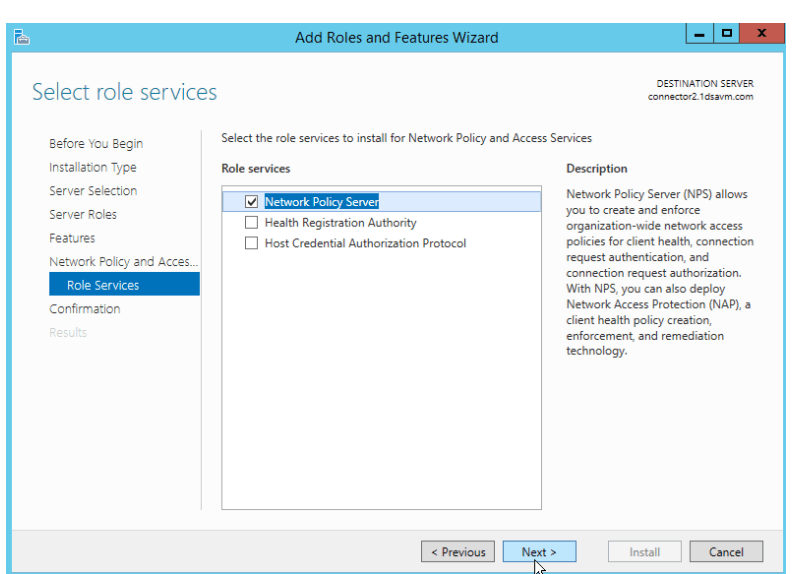
Download and Install the NPS Extension
- Go to Download NPS Extension for Azure MFA from Official Microsoft Download Center
- Download the NPS Extension for Azure MFA Installer.
- Run the installer
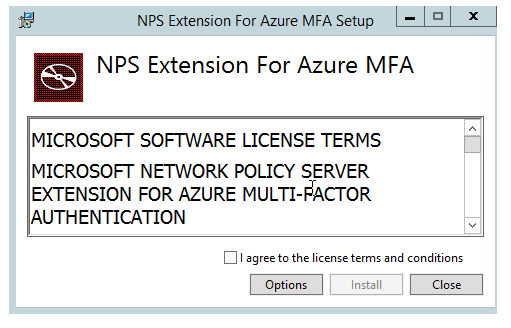
- Click Install
Configure the NPS Extension
- Run Windows Powershell as an Administrator
- At the powershell prompt, cd to “c:\Program Files\Microsoft\AzureMfa\Config”
- Run “.\AzureMfaNpsExtnConfigSetup.ps1”
- You will be prompted to authenticate with Azure.
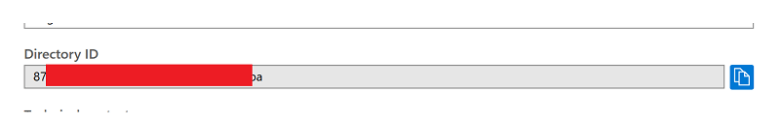
- After successful authentication, you will be prompted to enter your tenant id. This is your Directory ID which can be copied from your Azure Console:
- This script will create a self signed certificate for you.
Configure your NPS Server
- Access your NPS Server (via Admin Tools)
- Under standard configuration, select “Radius server for Dial-up or VPN Connections”
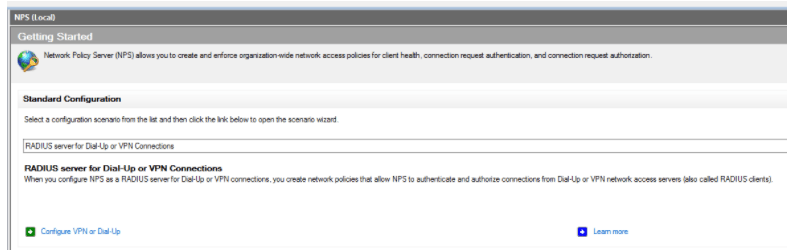
- Click Configure VPN or Dial-up
- Select “Virtual Private Network (VPN) Connections”
- Provide a friendly name ie. Workspace ONE
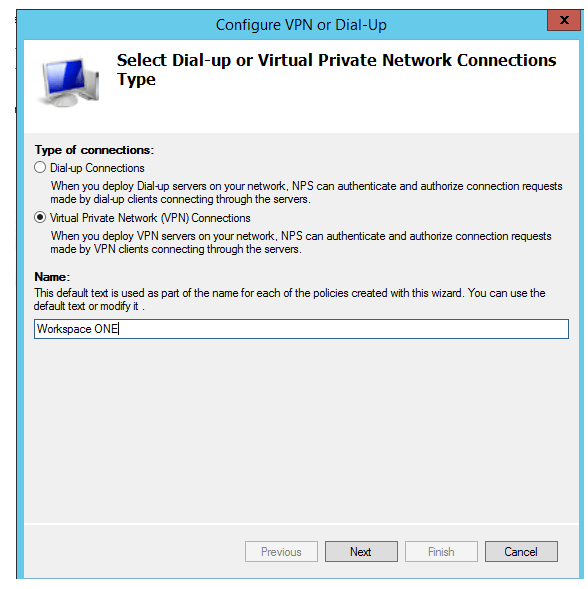
- Click Next
- Under Radius Clients -> Click Add
- Provide a friendly Name, IP Address and a Shared Secret
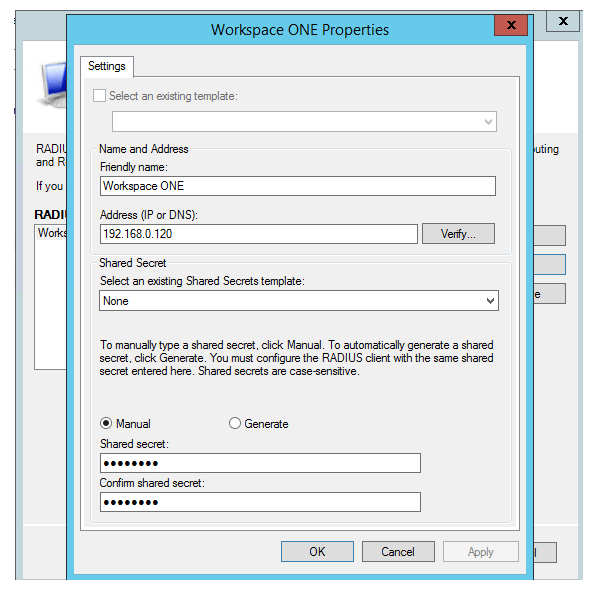
- Click OK and Next
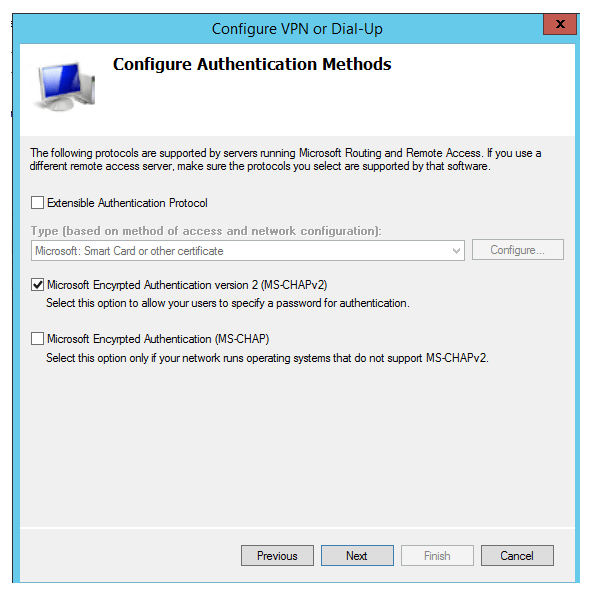
- Select Microsoft Encrypted Authentication version 2 (MS-CHAPv2)
- Click Next
- Under Groups, – Select a group that includes your MFA Users.
- Click Next for IP Filters
- Click Next for Encryption Settings
- Click Next for Realm Name (leave blank)
- Click Finish
- Click on Policies -> Connection Request Policies
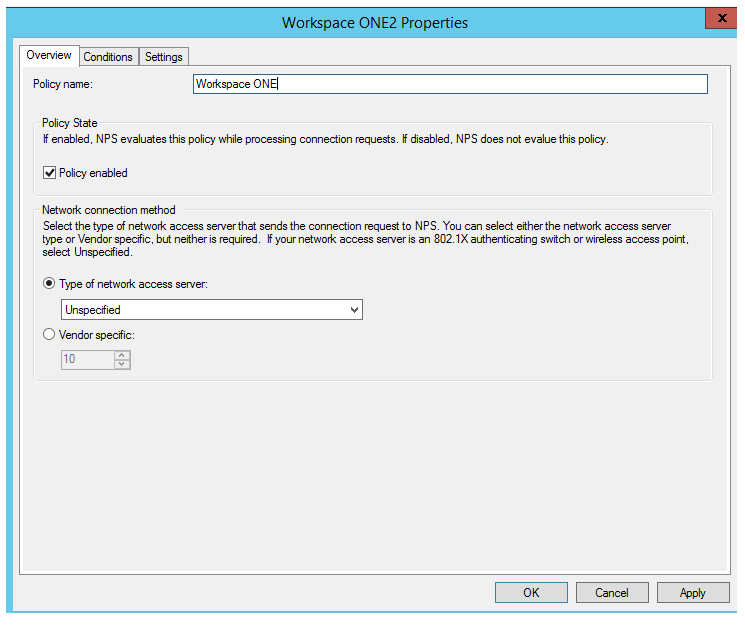
- Double Click on the new “Workspace ONE Policy”
- Change the type to Unspecified
- Click on the Condition Tab
- Delete the NAS Port Type and Click Add
- Select “Access Client IPv4Address”
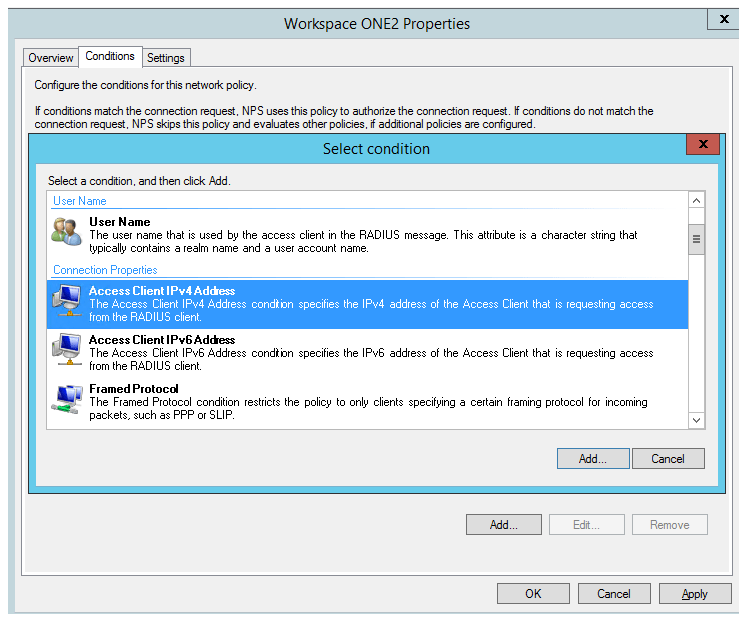
- Enter the IP Address of the Connector Server
- Click OK
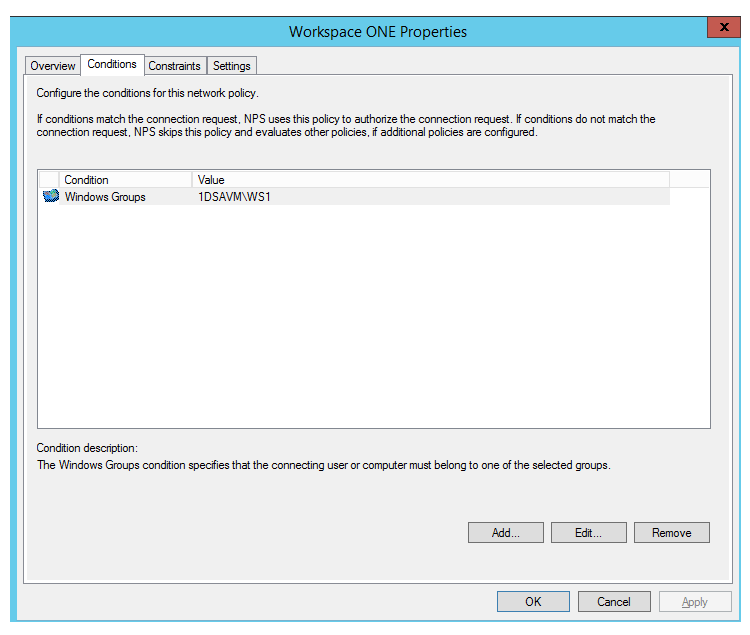
- Click on Policies -> Network Policies
- Double Click on the new “Workspace ONE Policy”
- Change the Type to Unspecified
- Under Conditions, you should just have the group condition
- Under Constraints, select “Microsoft Encrypted Authentication version 2 (MS-CHAP-v2)”
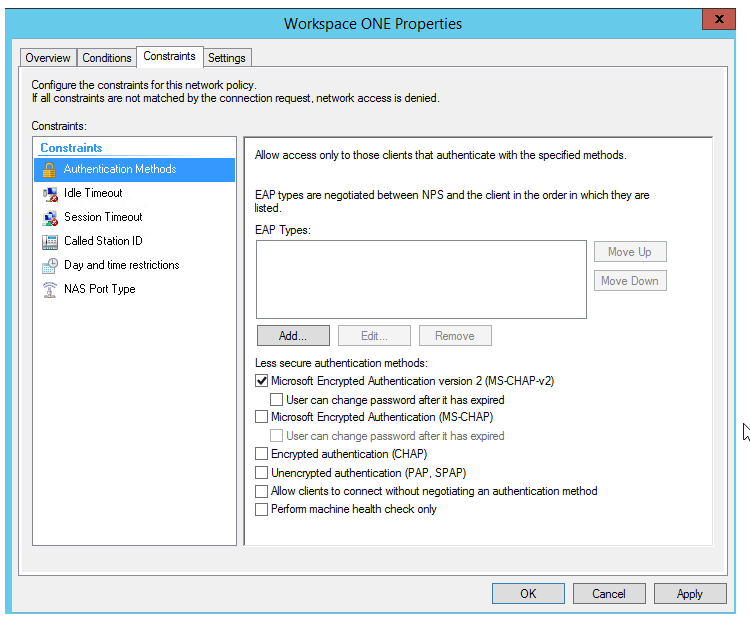
- Click OK.
Configure Workspace ONE Access
- Log into your Workspace ONE Access Admin Console
- Go to Identity & Access Manager -> Setup
- Click on your Connector Worker -> Auth Adapters
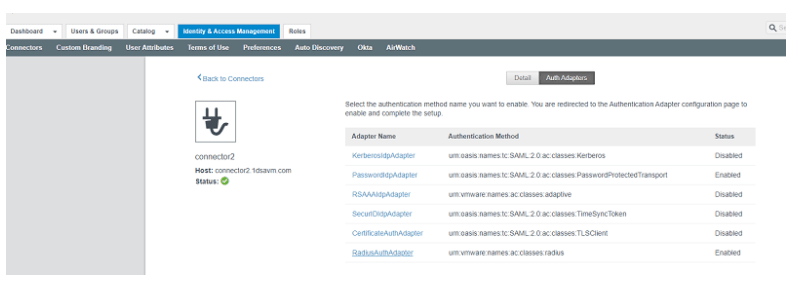
- Click on Radius Adapter
- Enter your Radius Host, Ports and Secret
Note: Do not enter an accounting port. I was not able to get this to work with the NPS Server.
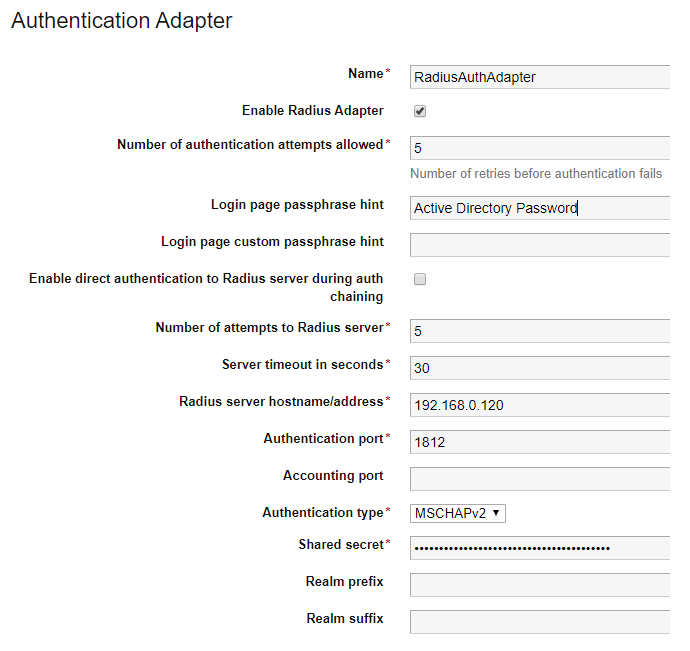
- Select MSChapv2 as the encryption type.
- Click Save
- In the Workspace ONE Access Console, go to Identity Providers and edit the Built-In provider.
- Enable the Cloud Based Radius Adapter
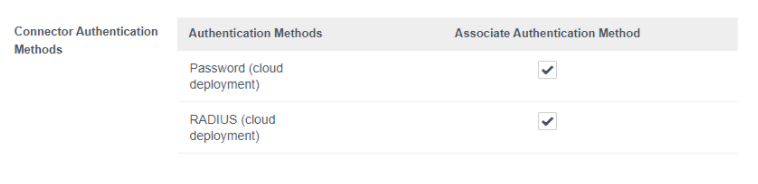
- Click Save.
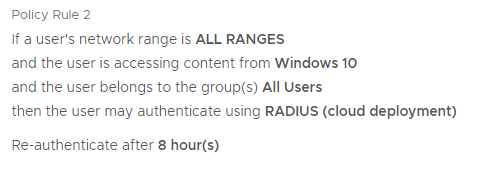
- You can now use the Cloud Radius Adapter in your Access Policies.
Thanks for the article.. How can I increase the Azure MFA timeout? Users are only given about 15 seconds to approve on the MS authenticator.. Are there any setting to increase this timeout value?
LikeLike
What device is the NPS client?
LikeLike
We used this tutorial to migrate from VMware Verify to MS Authenticator. After implementing this we are confronted with a second login for the VDI desktops. First login is email/password/MS authenticator, second login is for the desktop with username (already filled in) and password. How can we return to a single signon to our desktops?
LikeLike