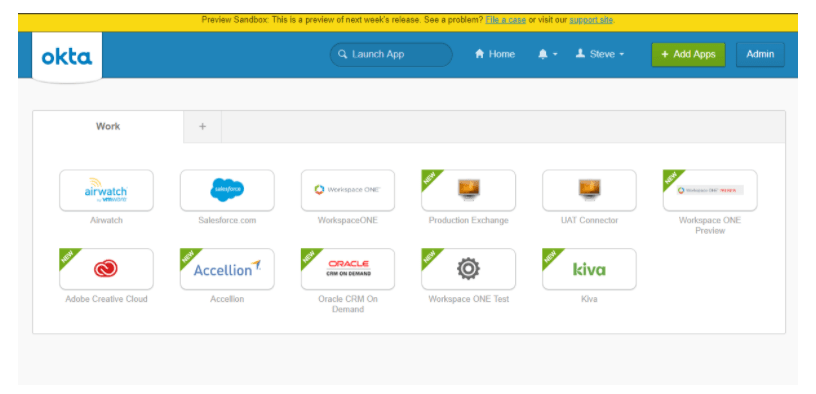
The release of Workspace ONE 19.03 brought in a very seamless integration of Okta Applications.
If you have integrated the two solutions previously you will recall the number of steps required to create and entitle new applications in Workspace from Okta. This integrations you to create and entitle applications in Okta and have them seamless appear in Workspace ONE along with your Native and Virtual Applications.
Lets walk through the steps to integrate the two solutions.
In this blog we are going to assume that you have existing connectors for Workspace ONE UEM and Workspace ONE Identity. We are also assuming you have your Workspace ONE Identity access policies already configured for Mobile SSO, Certificate or Password (Cloud Deployment).
Part 2: Unified Digital Workspace
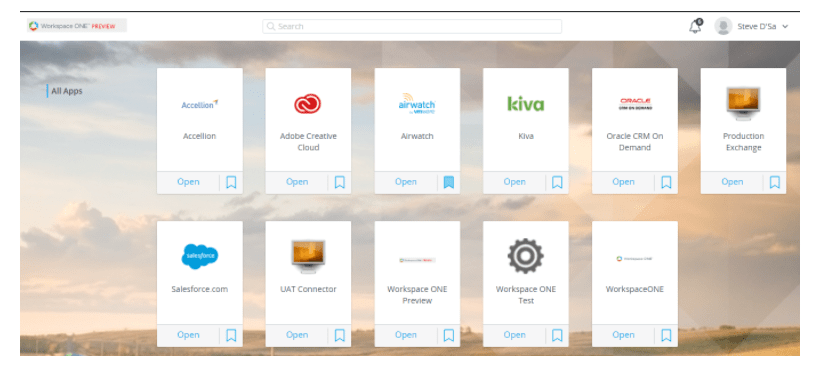
The objective of this section to automatically sync all SAML enabled applications from Okta to Workspace ONE. This configuration will eliminate the manual steps required to both create and entitle Okta applications in Workspace ONE.
Step 1: Create an Okta API Key
- Log into the Okta Admin Console
- Go to Security -> API

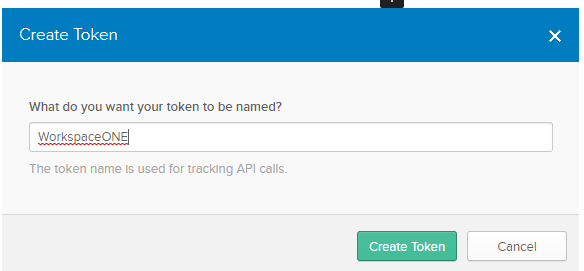
- Click Create Token
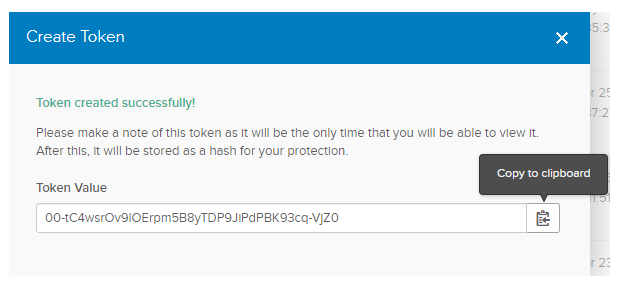
- Click the Copy Token button
Note: Its very important you copy and save this token somewhere. Once you close this window you will not be able to retrieve this value again. You will have to delete the token and create a new one.
Step 2: Configure Workspace ONE with Okta API Information
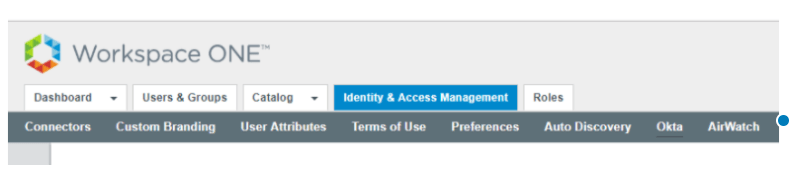
Note: If you are using Chrome, please be aware of Chrome auto filling any fields.
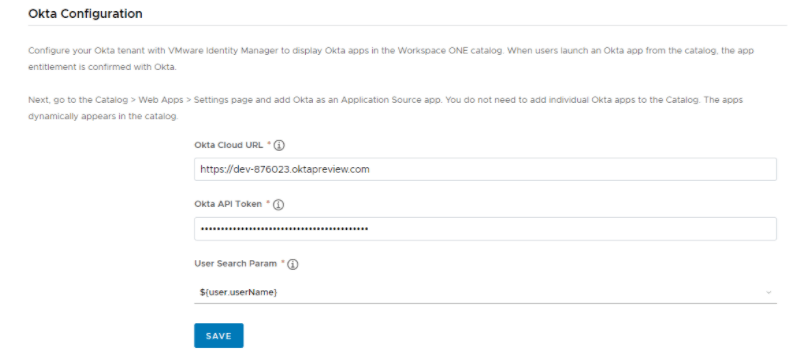
- Paste your Okta API Token
- Select the username search parameter that will match in Okta.
- Click Save
NOTE: Okta Applications will NOT appear in the Workspace ONE Admin Console
Step 3: Testing
- Log into Workspace ONE with a directory account.
- You should now see all your Okta Applications along with any other applications configured in Workspace ONE.

The Authentication Flow Explained
When you launch an Okta application from the Workspace ONE Console, it will use the configuration that has been setup in the Okta Application Source to send a SAML Response from Workspace ONE Access to Okta:
To your configured Okta Assertion Consumer URL (ACS), a SAML Response is posted along with a RelayState that will tell Okta which application the user should be sent to:

Okta will use the NameID in the Subject to appropriately map the user to a user within Okta:
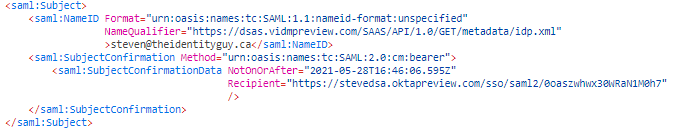
If you have configured an application sign-on policy that requires additional authentication, that will be triggered before the user is sent to the target application.
Hi ,
Wanted to open ws1 admin console in okta .
Any guide on this.
If there plz share to me on – ajaykadam445@gmail.com
LikeLike
Hi there – I currently don’t have a guide on how to do this but here are some high level steps:
1. Create a new “VMware Workspace ONE” Application in Okta
2. Add the RelayState (from the Sign-on Tab) so its equal to your admin interface ie. https://tenant.vidmpreview.com/SAAS/admin
3. Create a 3rd Party IDP in Workspace ONE Access using the metadata from the Sign-ON Tab on the app you just created in Okta.
3b. Create an AuthMethod such as OktaADMIN using passwordprotectedtransport
4. Create a fallback Auth method for OktaAdmin on your default access policy to allow for admin access. (Note: This fallback can be any number of levels deep as long as its present on the policy).
5. Assign the application in Okta
LikeLiked by 1 person
Thanks for this sir. I will try to do this on test environment will let you know.
LikeLike