Note: Please see my updated blog on Factor-Base Device Trust: https://theidentityguy.ca/2020/12/03/factor-based-device-trust-with-vmware-and-okta
If you have read my previous blog on configuring Configuring Device Trust, you will know that Okta has not yet implemented device trust for Windows and MacOS. I also mentioned in the previous blog that if you want to leverage device trust for Windows and MacOS that you will need to use the original method with just routing rules.
In my previous blog I didn’t go into the details on how you would configure device trust for both IOS/Android and Windows/MacOS. Its not really as straight forward as you would think because once you have configured an Identity Provider in Okta to use device trust, it will always send the device trust authentication context which will always result in an authentication failure for Windows and MacOS (assuming its being evaluated for Certificate and Device Compliance – AirWatch).
Note: This blog will not go into steps to configure Workspace ONE UEM or Workspace ONE Access to perform Certificate Based Authentication. We will assume that this has already been done.
There are a couple extra steps you will need to do. Lets walk through the steps.
Create a New Identity Provider
First you will need to create another Identity Provider for Workspace ONE.
- Log into the Okta Administration Portal and go to Security -> Identity Providers
- Click Add Identity Provider -> Add SAML 2.0 IDP
- Configure this Identity Provider exactly as you’ve configured the previous one
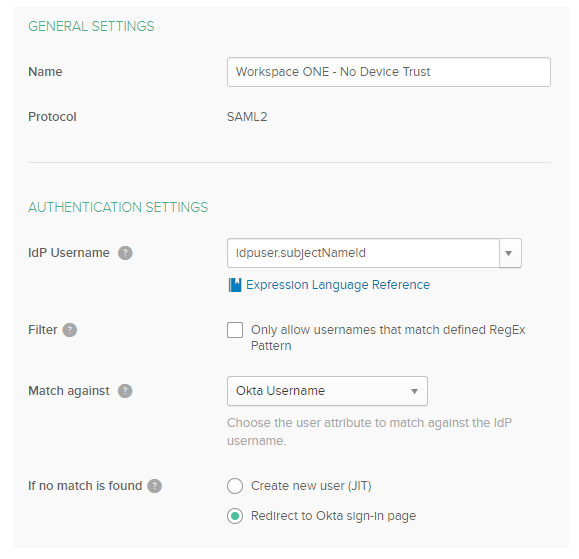
- Click on Show Advanced Settings
- Make sure the Request Authentication Context is set to None
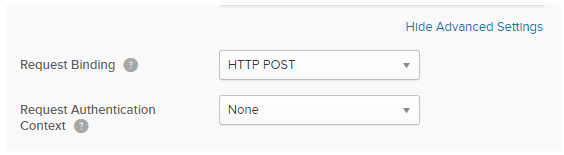
- Click Add Identity Provider
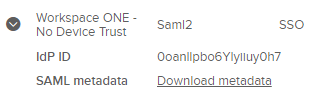
- Expand the Identity Provider you just created and download the metdata
Create a new Workspace ONE Application for Okta
- In Workspace ONE Access, got to Catalog and Click New
- Provide a name for this application (ie. Okta Device Trust for Windows/MacOS)
- Paste the metadata you downloaded in the previous step.
- Click Next, Next, Save
- Click Edit for the application you just created
- Click Configuration
- Modify to the username value to match the username format in Okta.
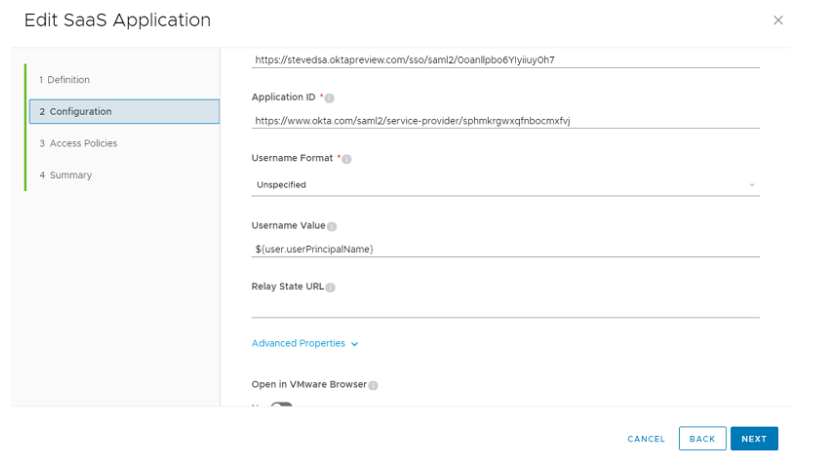
- Click Access Policies
- Select the same policy you assigned to the Okta Application Source
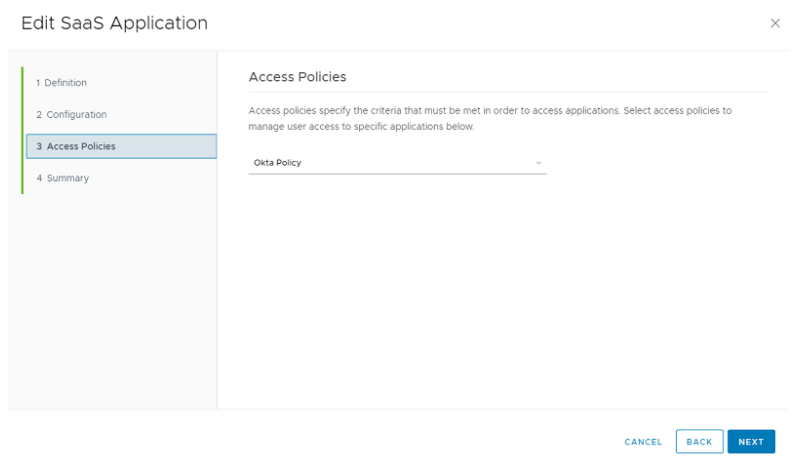
- Click Next – Save
- Assign the application to your users.
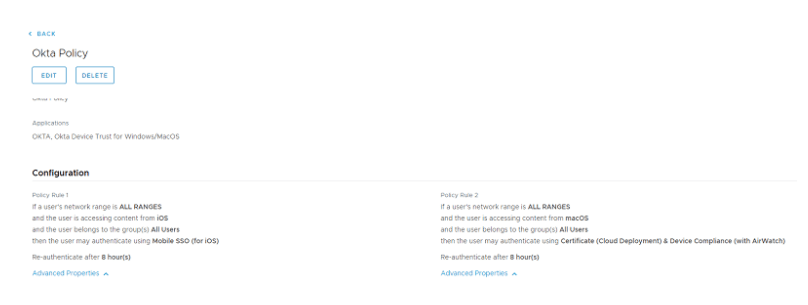
- Click on Identity and Access Management -> Policies
- Edit your Okta Policy
- Create a Policy Rule for MacOS to use Certificate and Device Compliance.
Modify your Routing Rules in Okta
Finally, we can now add this new configuration into the routing rules in Okta
- Log into the Okta Admin Console
- Click on Security -> Identity Providers
- Click on Routing Rules
- Click Add Routing Rule
- Add a rule that will evaluate Windows and MacOS for your required applications and select the new “Workspace ONE – No Device Trust” identity provider we created in the first step.
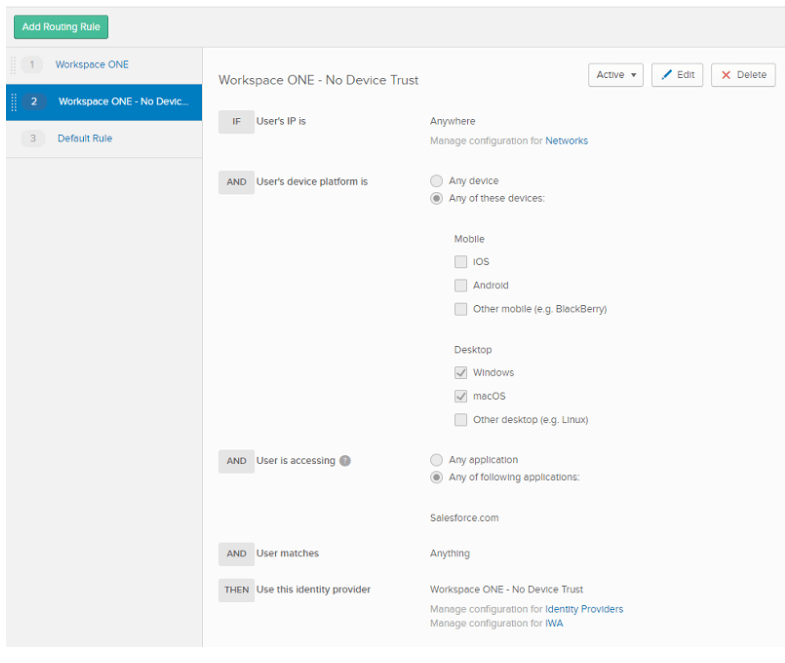
- Verify that there are no other rules that will take precedence over your newly created rule.