When troubleshooting SAML/OIDC, its extremely useful to have access to your HTTP headers to validate what is being passed from one provider to the next. This is very straight forward on Windows and MacOS devices but not quite as easy when we need the headers on a mobile device.
There are many tools on the market that can help proxy your mobile traffic. Most people default to Fiddler however I’ve personally had very little luck with fiddler for this purpose as Fiddler tends to truncate the SAML request thus making it useless for debugging SAML Traffic. I credit a former colleague of mine, Eugene for introducing me to a tool called MITM Proxy. As the name suggests, its a man in the middle product but useful in troubleshooting.
Please note – This is not an endorsement of this specific tool, its just a tool that I’ve had success with. The usual disclaimer with any third party product, please use at your own risk.
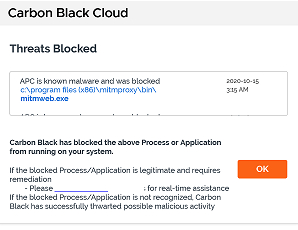
Before you start, make sure your Corporate IT department won’t block this tool as its quite common. You might see something like this:
Getting Started with MITM Proxy
- Download MITM Proxy from https://mitmproxy.org/
- Install MITM Proxy as per their instructions. https://docs.mitmproxy.org/stable/overview-installation/
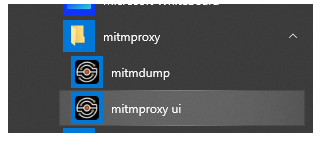
Note: Install this proxy on a system that is accessible by your mobile device. - Since running MITM Proxy on Windows 10, I will launch the MITM Proxy UI from the start menu.
- If everything goes well, you will see a CMD window displaying the proxy was successfully started and a browser tab open display the debug window.
- In my case, it doesn’t go well and I get the following error:
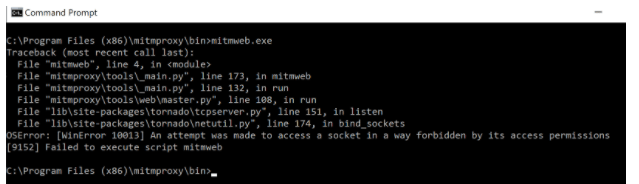
- This error does not necessarily mean your Corporate IT team is blocking the application (Although I’ve thought this many times). It most likely means you have a port conflict. Run a netstat and verify that 8080 and 8081 are not being used.
- If 8080 is taken, you will need to start this manually in a command window using a free port
C:\Program Files (x86)\mitmproxy\bin>mitmweb.exe –listen-port 8888 - If 8081 is taken, you will need to start this manually in a command window using a free port
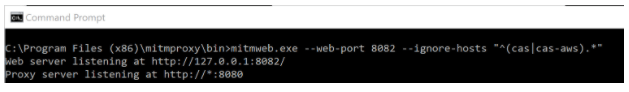
C:\Program Files (x86)\mitmproxy\bin>mitmweb.exe –web-port 8082
There is a way to make these changes permanent using YAML but I’ve not figured that out yet.
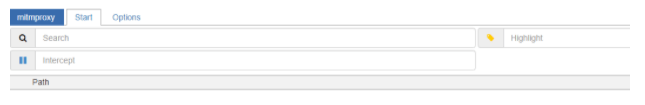
- Hopefully, you now have the application started and you see the console open in a web browser.
Setting up your IOS Device
- On your IOS Device, go to your Settings Application
- Click on WiFi
- Click the “i” beside your WiFi network
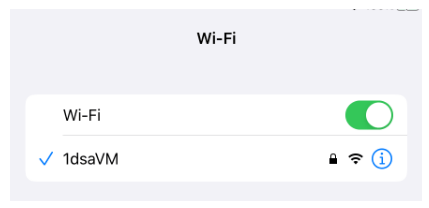
- Click on Configure Proxy at the bottom of the screen
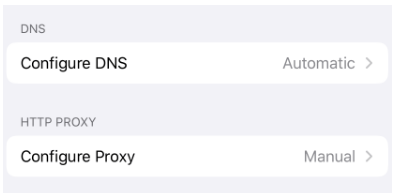
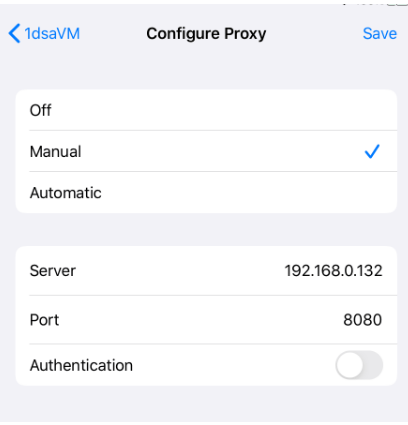
- Select Manual
- Enter the correct IP Address and Port
- Open Safari and verify that you can see traffic in the console by going to any http url ie. http://www.google.com (Ignore the connection is not private error).
Installing SSL Certificate for HTTPS Decryption
- Open Safari on your mobile device, and go to http://mitm.it
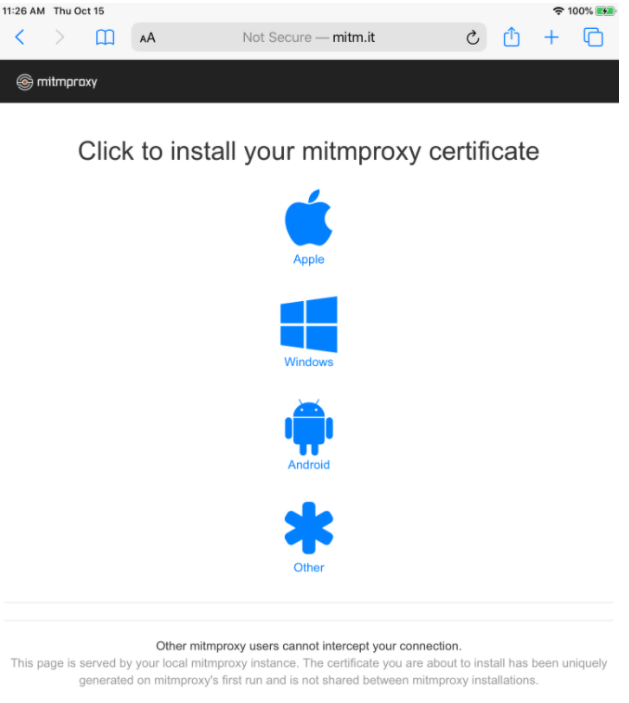
- Click on the Apple Link to download your profile.
- Go to your IOS Profiles and install the downloaded profile.
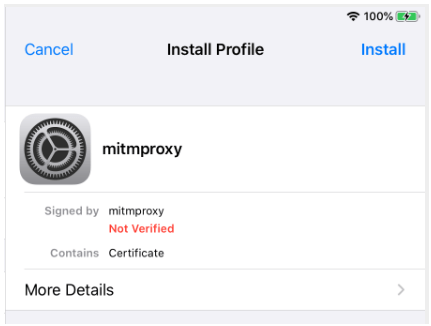
- In the Settings Application, Click on General -> About
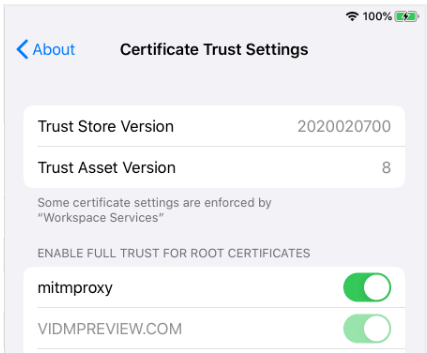
- Scroll down and click on “Certificate Trust Settings”
- Enable Full Trust for the MITM Proxy Certificate
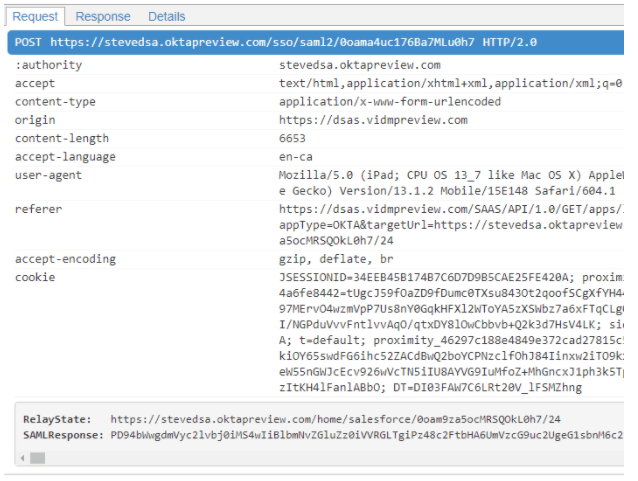
- You should now see full headers in your web console.
- You can use any online SAML Decoder to get full access to the SAML Requests/Responses
How to support Certificate Based Authentication
If you need to perform certificate based authentication, you can not ‘intercept’ a certificate challenge from the Workspace ONE CAS server. You will need to bypass the Cert Challenge from proxying through MITM
- Although you can modify settings on the fly using the UI, its probably easier to add the following switch when starting your MITM Proxy Server:
mitmweb.exe –web-port 8082 –ignore-hosts “^(cas|cas-aws).*”
I’m getting no internet connection on the wifi after setting the manual proxy
LikeLike