So in the latest integration between Workspace ONE Access (aka. VMware Identity Manager) and Okta, we’ve added the device trust capabilities into the Okta Administration Portals. I’ve noticed there has been some confusion on what this integration really does and why it’s been added to the solution.
Which method should you use? In order to determine which method you should use we need to look at both options.
Lets walk through how the process worked previously:
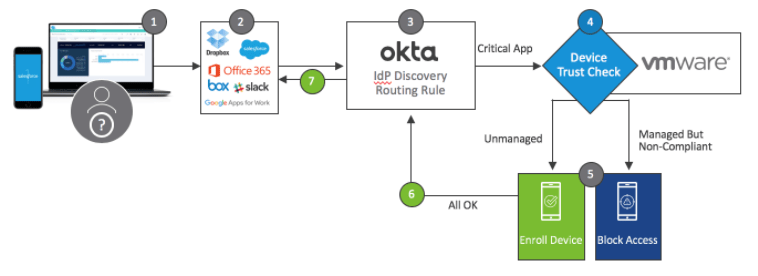
- User goes to a SaaS Application
- The SaaS application will redirect the user to Okta
- Okta Routing Rules will proxy the SAML Authentication request to Workspace ONE access based on the predefined rules.
- Workspace ONE Access will determine if the device is managed (based on Mobile SSO/Certificate) and if the device is compliant (based on the enrolment in Workspace ONE UEM)

- If the device meets correct conditions (both Managed and Compliant) it will send a SAML Authentication Response back to Okta where any additional sign-on policies will be triggered and the user will be returned to the SaaS application.
- If the device does not meet the correct conditions (both Managed and Compliant) the user will most likely be displayed an “Access Denied” error with any appropriate “Compliance” messaging.
The benefit of this option is that it can provide a detailed explanation of why the authentication failed. We can also configure Workspace ONE Access to integrate with an MFA solution to step up the authentication. The downside of using the existing method is that you need to configure authentication policies in both systems and the action to deny or MFA will apply to all application that Okta is routing to Workspace ONE Access.
Configuring Okta Device Trust
In the on going partnership between VMware and Okta, the strategy is to offload the authentication to Okta. This provides a strong value in configuring authentication policies in just one place.
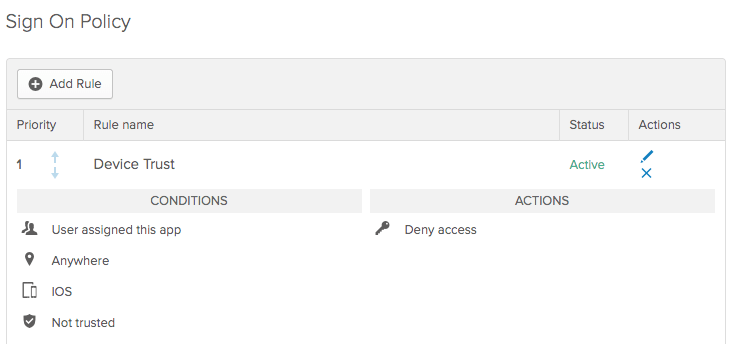
Once you configure device trust in Okta, you have the ability to configure sign-on policies on a per app basis. This provides a lot of value as there are some applications that you would want to straight out deny access and some that might be okay as long as we did a step up authentication.
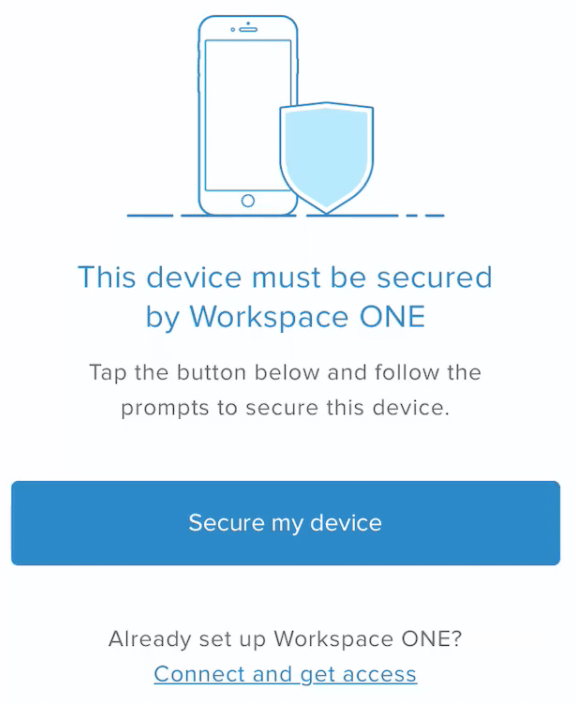
If you have configured a policy to DENY access, the user will be presented with the below message. They will have the ability to secure their device by enrolling in Workspace ONE UEM.
Let’s walk through the steps required to set this up and we’ll look under the covers of what is happening during the SAML exchange between the two systems.
First lets start in the Okta Portal,
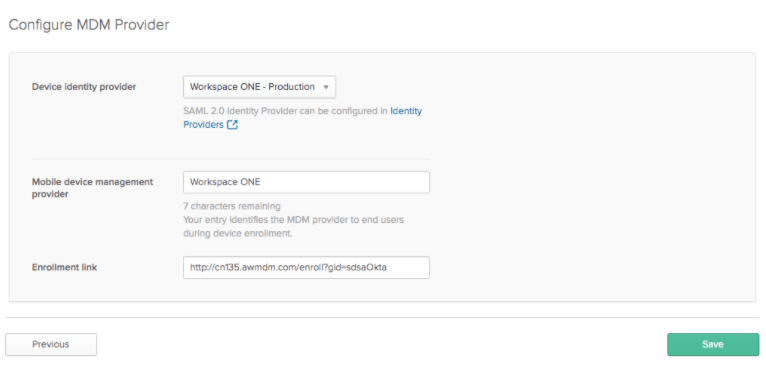
First you need to enable Device Trust. Under Security -> Device Trust, click EDIT for either IOS or Android.

- Enable IOS Device Trust
- Select “VMware”
- Select “SAML-based (Workspace ONE UEM + vIDM)
- Click Next
- Select the correct Identity Provider
- Provide a name such as “Workspace ONE”
- Enter either your Web Enrolment Link or a linked to the appropriate app store to download the Workspace ONE Intelligent Hub.
- Click Save
Now we can modify our sign-on policies for our applications. In your application specific sign-on policy, add a rule for either “IOS/Android” and select your appropriate device trust option and the correct action (DENY or MFA).
Finally, we have to configure the Identity Provider to send the correct flags to Workspace ONE Access in order to trigger the Device Trust.
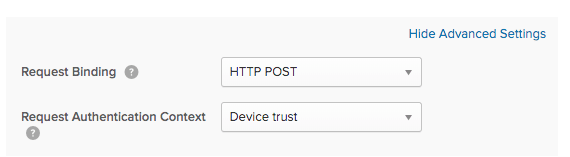
In Security -> Identity Providers, you need to enable the Device Trust Authentication Context. (Note: This is under Advanced Settings). I’ll explain shortly what this option is doing.
Configuring Workspace ONE Access for Okta Device Trust
We have to modify a couple setting in our Okta Application Source in order to support Okta Device Trust.
- Edit your Okta Application Source
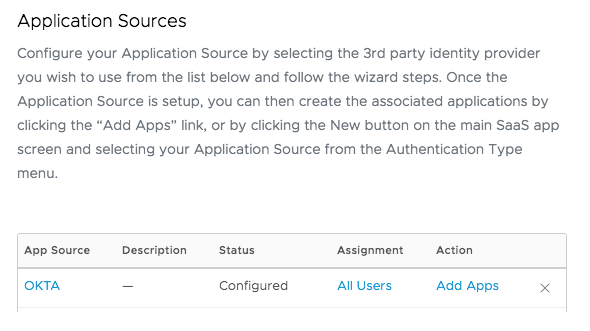
- Under Configuration, expand Advanced Properties
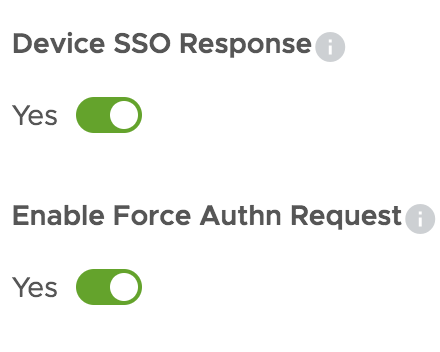
- Enable Device SSO Response
- Enable Force AuthN Request. This setting will allow Workspace ONE to accept an ForceAuthN in a SAML AuthN request and process the Device Trust Authentication Context. There are some implications of enabling this setting. We’ll discuss those later.
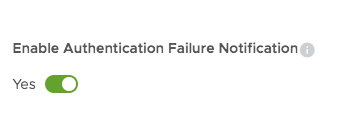
- Enable the Authentication Failure Notification. This setting will send a failure notification to Okta instead of display an error message on the Workspace ONE Access side.
- Click Next, Next, Save.
Understanding the SAML Exchange
When you make the changes above, the SAML messages between the two systems are modified.
When you configure the “Device Trust” authentication context in Okta, it will set a ForceAuthn flag = “True” in the AuthN request.
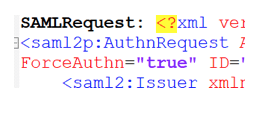
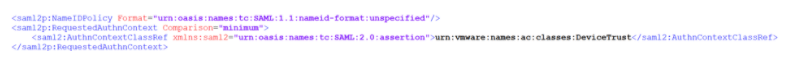
It will also add a device trust Authentication Context to the request:
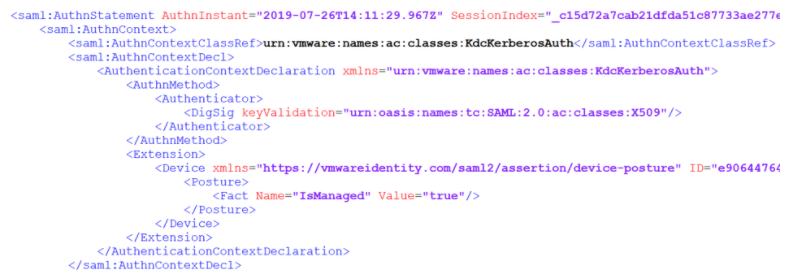
Workspace ONE Access will respond to Okta with the Authentication Class Reference that was used to authenticate the user along with the Device Posture Check. The Post Check returned will tell Okta whether the device is currently managed:
Implications of ForceAuthn
There are some important implications when using ForceAuthN in the Authentication Request. There are some Authentication Methods that are not supported. The most prominent ones are “Device Compliance” and your 3rd Party IDP authentication methods.
If you are using the Okta Device Trust, this means that you can NOT use the “Device Compliance” authentication method in Workspace ONE Access.
Device Compliance vs Device Trust
This is a very important distinction and might have an impact on which option your chose to enable Device Trust. In the current implementation (configuring Mobile SSO/Cert + Device Compliance) in Workspace ONE Access, it will validate that the device is managed and it will check the compliancy of the device in Workspace ONE UEM. In the initial release of Okta Device Trust, it will only check if the device is managed. Although this might seem like a big omission on the first release, depending on your compliance policies, you can imply that if a device is not compliant it will fail the posture check. (Removing MobileSSO profile on non-compliance).
Windows 10 and MacOS
In the first release of Okta Device Trust for Workspace ONE, they provided support for IOS and Android only. If you want Device Trust for Windows 10 and MacOS, you need to use the current method of configuring Cert + Device Compliance in Workspace ONE Access.
One thought on “Workspace ONE – Okta Integration Part 4: Device Trust”